EISA configuration is a Dell partition that is supposed to be hidden and not take up any of the letters. Research shows that running some emulation software and/or some partitioning utilities can "unhide" it and exhibit the behavior you're seeing. Also, rootkits can corrupt the boot configuration and do the same thing. I have been unable to find a solution other than sometimes when the emulation software is uninstalled, things return to normal. Other times I can find that if the rootikit is removed, the partition again "hides'.
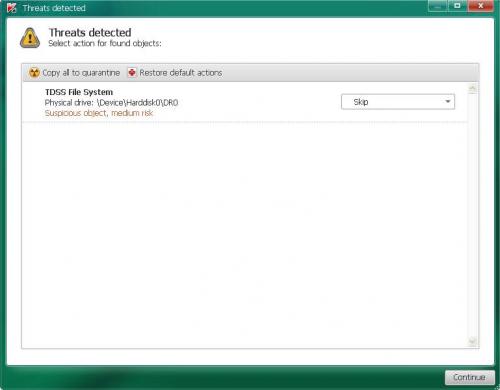
Even though some tools say that your Master Boot Record (MBR) may be infected, when I scanned it, it appeared clean and some tools say it is clean. Kaspersky has been the program that has had greatest success in restoring the hidden partition to normal... but when we ran TDSSkiller, it did not give you the option of curing, which would "correct" the MBR.
My honest opinion, due to the fact that this has been an ongoing issue since at least November, and in each case there has been at least traces pointing to rootkits..., your best course of action would be to to a reformat of your main drive and reinstall your operating system.
Because you have a dell... you would need the Dell disk to do this - you would probably have to get this from Dell. I understand the charge a nominal fee for this.
You cannot use the full XP disk because your product key will only work with the Dell OEM disk.
You should be able to remove your new drive and leave as is... but you would lose anything on the main drive in the formatting process so you need to have a good backup before proceeding.
Anyhow, that's my best advice. Other than that we could try TDSSkiller again and see if it will cure this time. Or, and not my recommendation because of the possibility of a rootkit as the culprit, you can just point your shortcuts that are now looking for the G: drive to the I: drive. You do this by right clicking on the shortcut and changing the G: in the target to I:.



 This topic is locked
This topic is locked