[Resolved] Computer Hijacked
#1
![[Resolved] Computer Hijacked: post #1](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 23 September 2009 - 06:51 PM
Register to Remove
#2
![[Resolved] Computer Hijacked: post #2](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 23 September 2009 - 07:54 PM
#3
![[Resolved] Computer Hijacked: post #3](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 26 September 2009 - 11:15 PM
Please download exeHelper to your desktop.
- Double-click on exeHelper.com to run the fix.
- A black window should pop up, press any key to close once the fix is completed.
- Post the contents of log.txt (Will be created in the directory where you ran exeHelper.com)
NEXT
Please save this file to your desktop.
- Click on Start > Run, and copy-paste the following command (the bolded text) into the open run box, then click OK.
"%userprofile%\desktop\win32kdiag.exe" -f -r
- When it's finished, there will be a log called Win32kDiag.txt on your desktop.
- Please open it with notepad and post the contents here.
Microsoft MVP 2010, 2011, 2012, 2013, 2014, 2015
#4
![[Resolved] Computer Hijacked: post #4](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 27 September 2009 - 08:46 AM
#5
![[Resolved] Computer Hijacked: post #5](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 27 September 2009 - 08:52 AM
Microsoft MVP 2010, 2011, 2012, 2013, 2014, 2015
#6
![[Resolved] Computer Hijacked: post #6](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 27 September 2009 - 12:48 PM
#7
![[Resolved] Computer Hijacked: post #7](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 27 September 2009 - 12:51 PM
Please do the following:
Download Combofix from either of the links below. You must rename it to combo-fix.exe before saving it.
Save it to your desktop.
**Note: In the event you already have Combofix, delete it, this is a new version that I need you to download. It is important that it is saved and renamed following this process directly to your desktop**
- If you are using Firefox, make sure that your download settings are as follows:
- Tools->Options->Main tab
- Set to "Always ask me where to Save the files".
Link 1
Link 2
-----------------------------------------------------------
- Very Important! Temporarily disable your anti-virus, script blocking and any anti-malware real-time protection before performing a scan. They can interfere with ComboFix or remove some of its embedded files which may cause "unpredictable results".
- Click on this link to see a list of programs that should be disabled. The list is not all inclusive. If yours is not listed and you don't know how to disable it, please ask.
-----------------------------------------------------------
- NOTE: If ComboFix asks to install the Recovery Console, please ALLOW it to do so.
-----------------------------------------------------------
- Double click on the renamed ComboFix.exe & follow the prompts. When finished, it will produce a report for you.
- Please post the C:\ComboFix.txt so we can continue cleaning the system.
-----------------------------------------------------------
Microsoft MVP 2010, 2011, 2012, 2013, 2014, 2015
#8
![[Resolved] Computer Hijacked: post #8](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 27 September 2009 - 01:43 PM
Microsoft Windows XP Professional 5.1.2600.3.1252.1.1033.18.1535.930 [GMT -5:00]
Running from: c:\documents and settings\Dennis\Desktop\Combo-Fix.exe
AV: McAfee VirusScan *On-access scanning disabled* (Updated) {84B5EE75-6421-4CDE-A33A-DD43BA9FAD83}
FW: McAfee Personal Firewall *disabled* {94894B63-8C7F-4050-BDA4-813CA00DA3E8}
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
c:\$recycle.bin\S-1-5-21-3512529902-1577875902-252900521-1000
c:\documents and settings\All Users\Application Data\diquke.com
c:\documents and settings\All Users\Application Data\ejudilo.ban
c:\documents and settings\All Users\Application Data\jujudoxot.bat
c:\documents and settings\All Users\Application Data\loqulizi.exe
c:\documents and settings\All Users\Application Data\majaginy.pif
c:\documents and settings\All Users\Application Data\ojufonulyp._sy
c:\documents and settings\All Users\Application Data\ujukate.vbs
c:\documents and settings\All Users\Application Data\unujehaxat.lib
c:\documents and settings\All Users\Application Data\uzuky.dll
c:\documents and settings\All Users\Application Data\vawip.reg
c:\documents and settings\All Users\Application Data\xaxeqovyq.bin
c:\documents and settings\All Users\Application Data\xuso.scr
c:\documents and settings\All Users\Application Data\zerybyx.lib
c:\documents and settings\All Users\Documents\azorif.exe
c:\documents and settings\All Users\Documents\firoqe._dl
c:\documents and settings\All Users\Documents\gowuxepi._dl
c:\documents and settings\All Users\Documents\hafociceja._dl
c:\documents and settings\All Users\Documents\rekavefeku.exe
c:\documents and settings\All Users\Documents\telib.scr
c:\documents and settings\All Users\Documents\ukogu.inf
c:\documents and settings\All Users\Documents\zyfakiq.dl
c:\documents and settings\All Users\Start Menu\HP Image Zone .lnk
c:\documents and settings\Dennis\Application Data\awuheze.inf
c:\documents and settings\Dennis\Application Data\esecotehy.vbs
c:\documents and settings\Dennis\Application Data\olafe.dll
c:\documents and settings\Dennis\Application Data\qojohogyry._dl
c:\documents and settings\Dennis\Application Data\rahyhit._dl
c:\documents and settings\Dennis\Application Data\tenilucag.sys
c:\documents and settings\Dennis\Application Data\ukiv.com
c:\documents and settings\Dennis\Application Data\xehoce.ban
c:\documents and settings\Dennis\Application Data\zybowi.bat
c:\documents and settings\Dennis\Cookies\apofi._dl
c:\documents and settings\Dennis\Cookies\cycuhopyb.pif
c:\documents and settings\Dennis\Cookies\ivanyp.inf
c:\documents and settings\Dennis\Cookies\iwejece.bat
c:\documents and settings\Dennis\Cookies\kazic.lib
c:\documents and settings\Dennis\Cookies\micivavop.dll
c:\documents and settings\Dennis\Cookies\nugopohu.dat
c:\documents and settings\Dennis\Cookies\osicycyr.scr
c:\documents and settings\Dennis\Cookies\qimehotubo.com
c:\documents and settings\Dennis\Cookies\tazig.reg
c:\documents and settings\Dennis\Cookies\ujydu.sys
c:\documents and settings\Dennis\Local Settings\Application Data\ceziwo._dl
c:\documents and settings\Dennis\Local Settings\Application Data\ipunapipaq.vbs
c:\documents and settings\Dennis\Local Settings\Application Data\lolevano.ban
c:\documents and settings\Dennis\Local Settings\Application Data\omys.dl
c:\documents and settings\Dennis\Local Settings\Application Data\ozibu.bat
c:\documents and settings\Dennis\Local Settings\Application Data\pagi.exe
c:\documents and settings\Dennis\Local Settings\Application Data\ucop.exe
c:\documents and settings\Dennis\Local Settings\Application Data\ucurazesy.bin
c:\documents and settings\Dennis\Local Settings\Application Data\uluqos.bat
c:\documents and settings\Dennis\Local Settings\Application Data\vobyde.sys
c:\documents and settings\Dennis\Local Settings\Application Data\ykosexukyk._dl
c:\documents and settings\Dennis\Local Settings\Application Data\ysej.bat
c:\documents and settings\Dennis\Local Settings\Temporary Internet Files\badol.reg
c:\documents and settings\Dennis\Local Settings\Temporary Internet Files\etice.ban
c:\documents and settings\Dennis\Local Settings\Temporary Internet Files\fevow.sys
c:\documents and settings\Dennis\Local Settings\Temporary Internet Files\jytifada.db
c:\documents and settings\Dennis\Local Settings\Temporary Internet Files\nyxovafu.inf
c:\documents and settings\Dennis\Local Settings\Temporary Internet Files\ozymuvolej.vbs
c:\documents and settings\Dennis\Local Settings\Temporary Internet Files\uhite._sy
c:\documents and settings\Dennis\Local Settings\Temporary Internet Files\wokynymy.dll
c:\documents and settings\Dennis\Local Settings\Temporary Internet Files\yhubativ.com
c:\documents and settings\Dennis\Local Settings\Temporary Internet Files\yletija.dl
c:\program files\Common Files\hybyvu.com
c:\program files\Common Files\niwodaw.vbs
c:\program files\Common Files\obyxad.exe
c:\program files\Common Files\yfiqigo.dl
c:\program files\Common Files\zyvolaf.sys
c:\program files\INSTALL.LOG
c:\windows\face.dl
c:\windows\facynizyno.dl
c:\windows\ihicimupo.scr
c:\windows\ihumovo.dll
c:\windows\ikini._dl
c:\windows\Installer\WMEncoder.msi
c:\windows\rudi.bin
c:\windows\sane.dll
c:\windows\system32\barafihy.dl
c:\windows\system32\drivers\ndisrd.sys
c:\windows\system32\epygimi.sys
c:\windows\system32\ndisapi.dll
c:\windows\system32\ntnet.drv
c:\windows\system32\odogo.inf
c:\windows\system32\ofikuwen.bat
c:\windows\system32\serufoc.pif
c:\windows\system32\sstray.exe
c:\windows\system32\twain.dll
c:\windows\system32\utyg.reg
c:\windows\system32\vytivopuqo.bin
c:\windows\system32\weme._dl
c:\windows\tygimijek.dl
c:\windows\tyriw.dll
c:\windows\uhukucoku._dl
c:\windows\werogyn.vbs
c:\windows\wpd99.drv
c:\windows\xatu.vbs
c:\windows\xawikabicy.vbs
c:\windows\xery.dl
c:\windows\ybevam.dl
c:\windows\ylolehory.vbs
c:\windows\zupukady.bat
c:\windows\system32\proquota.exe was missing
Restored copy from - c:\windows\ServicePackFiles\i386\proquota.exe
.
((((((((((((((((((((((((((((((((((((((( Drivers/Services )))))))))))))))))))))))))))))))))))))))))))))))))
.
-------\Legacy_NDISRD
-------\Legacy_{79007602-0CDB-4405-9DBF-1257BB3226ED}
-------\Legacy_{79007602-0CDB-4405-9DBF-1257BB3226EE}
((((((((((((((((((((((((( Files Created from 2009-08-27 to 2009-09-27 )))))))))))))))))))))))))))))))
.
2009-09-27 19:11 . 2008-04-14 00:12 50176 -c--a-w- c:\windows\system32\dllcache\proquota.exe
2009-09-27 19:11 . 2008-04-14 00:12 50176 ----a-w- c:\windows\system32\proquota.exe
2009-09-27 17:56 . 2009-09-27 17:56 -------- d-sh--w- c:\documents and settings\Dennis\IECompatCache
2009-09-27 17:54 . 2009-09-27 17:54 -------- d-sh--w- c:\documents and settings\Dennis\PrivacIE
2009-09-27 17:31 . 2008-04-13 19:18 52480 -c--a-w- c:\windows\system32\dllcache\i8042prt.sys
2009-09-27 17:31 . 2008-04-13 19:18 52480 ----a-w- c:\windows\system32\drivers\i8042prt.sys
2009-09-27 17:28 . 2009-09-27 17:28 -------- d-sh--w- c:\documents and settings\LocalService\IETldCache
2009-09-27 17:27 . 2009-09-27 17:27 -------- d-sh--w- c:\documents and settings\Dennis\IETldCache
2009-09-27 16:58 . 2009-09-27 16:58 -------- d-----w- C:\$dpx$.tmp
2009-09-27 04:32 . 2009-08-07 08:48 100352 -c----w- c:\windows\system32\dllcache\iecompat.dll
2009-09-27 04:32 . 2009-09-27 04:32 -------- d-----w- c:\windows\ie8updates
2009-09-27 04:31 . 2009-07-03 17:09 12800 -c----w- c:\windows\system32\dllcache\xpshims.dll
2009-09-27 04:31 . 2009-07-03 17:09 246272 -c----w- c:\windows\system32\dllcache\ieproxy.dll
2009-09-27 04:29 . 2009-09-27 04:31 -------- dc-h--w- c:\windows\ie8
2009-09-27 00:44 . 2009-07-08 18:44 79816 ----a-w- c:\windows\system32\drivers\mfeavfk.sys
2009-09-27 00:44 . 2009-07-08 18:44 40552 ----a-w- c:\windows\system32\drivers\mfesmfk.sys
2009-09-27 00:44 . 2009-07-08 18:44 35272 ----a-w- c:\windows\system32\drivers\mfebopk.sys
2009-09-27 00:44 . 2009-07-16 17:32 120136 ----a-w- c:\windows\system32\drivers\Mpfp.sys
2009-09-27 00:43 . 2009-09-27 00:44 -------- d-----w- c:\program files\Common Files\McAfee
2009-09-27 00:43 . 2009-09-27 00:43 -------- d-----w- c:\program files\McAfee.com
2009-09-27 00:43 . 2009-09-27 17:43 -------- d-----w- c:\program files\McAfee
2009-09-27 00:39 . 2009-07-08 18:43 34248 ----a-w- c:\windows\system32\drivers\mferkdk.sys
2009-09-25 04:34 . 2009-09-25 04:34 16520 ----a-w- c:\windows\system32\nigun.dat
2009-09-25 03:44 . 2009-09-25 03:44 14043 ----a-w- c:\windows\system32\fozyreg.dat
2009-09-25 03:44 . 2009-09-25 03:44 16147 ----a-w- c:\program files\Common Files\wolydycud.dat
2009-09-25 03:44 . 2009-09-25 03:44 17090 ----a-w- c:\windows\jemutogeh.dat
2009-09-25 03:39 . 2009-09-25 03:39 128352 ----a-w- c:\windows\system32\0fb49.dll
2009-09-25 03:39 . 2009-09-25 03:39 54624 ----a-w- c:\windows\system32\0fb49.sys
2009-09-25 03:18 . 2009-09-25 03:18 15840 ----a-w- c:\program files\Common Files\naneg.dat
2009-09-24 03:21 . 2009-09-24 03:21 11495 ----a-w- c:\windows\ijyjodiw.com
2009-09-24 03:21 . 2009-09-24 03:21 14703 ----a-w- c:\windows\tuxawuni.com
2009-09-24 01:30 . 2009-09-24 01:30 -------- d-----w- c:\program files\Trend Micro
2009-09-24 00:32 . 2009-09-24 00:32 -------- d-----w- c:\documents and settings\All Users\Application Data\SITEguard
2009-09-24 00:32 . 2009-09-24 00:32 -------- d-----w- c:\program files\STOPzilla!
2009-09-24 00:32 . 2009-09-24 00:32 -------- d-----w- c:\program files\Common Files\iS3
2009-09-24 00:32 . 2009-09-24 00:33 -------- d-----w- c:\documents and settings\All Users\Application Data\STOPzilla!
2009-09-24 00:11 . 2009-09-10 19:54 38224 ----a-w- c:\windows\system32\drivers\mbamswissarmy.sys
2009-09-24 00:11 . 2009-09-26 04:11 -------- d-----w- c:\program files\Malwarebytes' Anti-Malware
2009-09-24 00:11 . 2009-09-10 19:53 19160 ----a-w- c:\windows\system32\drivers\mbam.sys
2009-09-23 04:28 . 2009-09-23 04:28 -------- d-----w- c:\documents and settings\Dennis\Application Data\Malwarebytes
2009-09-23 04:28 . 2009-09-23 04:28 -------- d-----w- c:\documents and settings\All Users\Application Data\Malwarebytes
2009-09-22 02:51 . 2009-09-22 02:51 93632 ----a-w- c:\documents and settings\LocalService\Local Settings\Application Data\FontCache3.0.0.0.dat
2009-09-22 02:49 . 2009-09-22 02:49 -------- d-----w- c:\documents and settings\Dennis\Local Settings\Application Data\Apple_Inc
2009-09-17 02:06 . 2009-09-17 02:06 -------- d-----w- c:\program files\iPhone Configuration Utility
2009-09-17 02:01 . 2009-09-17 02:01 -------- d-----w- c:\program files\iPod
2009-09-17 02:00 . 2009-09-17 02:03 -------- d-----w- c:\program files\iTunes
2009-09-17 02:00 . 2009-09-17 02:03 -------- d-----w- c:\documents and settings\All Users\Application Data\{755AC846-7372-4AC8-8550-C52491DAA8BD}
2009-09-10 01:55 . 2009-06-21 21:44 153088 -c----w- c:\windows\system32\dllcache\triedit.dll
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2009-09-27 17:53 . 2008-12-25 23:21 -------- d-----w- c:\documents and settings\Dennis\Application Data\MioNet
2009-09-27 00:57 . 2009-07-26 13:48 -------- d-----w- c:\documents and settings\All Users\Application Data\McAfee
2009-09-27 00:46 . 2008-12-25 23:20 -------- d-----w- c:\program files\MioNet
2009-09-26 04:04 . 2006-12-12 04:35 -------- d-----w- c:\program files\Windows Defender
2009-09-26 04:03 . 2008-02-29 14:23 -------- d-----w- c:\program files\ICQ
2009-09-25 04:34 . 2009-09-25 04:34 11700 ----a-w- c:\documents and settings\All Users\Application Data\femapoh.dat
2009-09-25 03:01 . 2009-09-25 03:01 16573 ----a-w- c:\documents and settings\All Users\Application Data\ocuwyp.dat
2009-09-25 01:17 . 2009-09-25 01:17 17406 ----a-w- c:\program files\Common Files\yfanu.lib
2009-09-17 02:35 . 2006-09-15 03:27 -------- d-----w- c:\documents and settings\Dennis\Application Data\Apple Computer
2009-09-17 02:01 . 2007-10-18 01:03 -------- d-----w- c:\program files\Common Files\Apple
2009-09-17 01:56 . 2006-09-15 03:27 -------- d-----w- c:\program files\QuickTime
2009-09-17 00:47 . 2006-11-13 02:25 -------- d-----w- c:\program files\Java
2009-09-05 20:16 . 2007-12-27 03:18 -------- d-----w- c:\documents and settings\Dennis\Application Data\Azureus
2009-08-29 00:42 . 2008-09-11 01:23 2065696 ----a-w- c:\windows\system32\usbaaplrc.dll
2009-08-29 00:42 . 2007-10-18 01:03 40448 ----a-w- c:\windows\system32\drivers\usbaapl.sys
2009-08-26 14:09 . 2009-08-25 18:49 -------- d-----w- c:\program files\Total 3D Home
2009-08-25 20:43 . 2009-08-25 20:43 -------- d-----w- c:\documents and settings\Dennis\Application Data\Individual Software
2009-08-25 19:30 . 2009-08-25 18:49 -------- d-----w- c:\program files\Common Files\Individual Software
2009-08-25 19:28 . 2009-08-25 19:28 -------- d-----w- c:\documents and settings\All Users\Application Data\Individual Software
2009-08-20 22:22 . 2006-11-29 01:56 -------- d-----w- c:\documents and settings\All Users\Application Data\SnapStream
2009-08-20 22:21 . 2006-11-29 01:50 -------- d-----w- c:\program files\SnapStream Media
2009-08-15 08:29 . 2006-09-14 04:30 33504 ----a-w- c:\documents and settings\Dennis\Local Settings\Application Data\GDIPFONTCACHEV1.DAT
2009-08-15 08:10 . 2009-08-15 08:10 -------- d-----w- c:\program files\MSBuild
2009-08-15 08:10 . 2009-08-15 08:10 -------- d-----w- c:\program files\Reference Assemblies
2009-08-08 02:37 . 2007-12-27 03:17 -------- d-----w- c:\program files\Azureus
2009-08-05 09:01 . 2001-08-23 12:00 204800 ----a-w- c:\windows\system32\mswebdvd.dll
2009-07-25 10:23 . 2009-02-22 17:29 411368 ----a-w- c:\windows\system32\deploytk.dll
2009-07-20 19:57 . 2009-07-20 19:57 17408 ----a-r- c:\windows\system32\SZIO5.dll
2009-07-20 19:56 . 2009-07-20 19:56 311296 ----a-r- c:\windows\system32\SZBase5.dll
2009-07-20 19:56 . 2009-07-20 19:56 540672 ----a-r- c:\windows\system32\SZComp5.dll
2009-07-17 19:01 . 2001-08-23 12:00 58880 ----a-w- c:\windows\system32\atl.dll
2009-07-14 04:43 . 2006-09-14 04:19 286208 ----a-w- c:\windows\system32\wmpdxm.dll
2009-07-09 20:52 . 2009-07-09 20:52 126976 ----a-r- c:\windows\system32\IS3HTUI5.dll
2009-07-09 20:52 . 2009-07-09 20:52 393216 ----a-r- c:\windows\system32\IS3DBA5.dll
2009-07-09 20:51 . 2009-07-09 20:51 385024 ----a-r- c:\windows\system32\IS3UI5.dll
2009-07-09 20:51 . 2009-07-09 20:51 61440 ----a-r- c:\windows\system32\IS3Hks5.dll
2009-07-09 20:51 . 2009-07-09 20:51 23040 ----a-r- c:\windows\system32\IS3XDat5.dll
2009-07-09 20:50 . 2009-07-09 20:50 225280 ----a-r- c:\windows\system32\IS3Win325.dll
2009-07-09 20:50 . 2009-07-09 20:50 94208 ----a-r- c:\windows\system32\IS3Inet5.dll
2009-07-09 20:50 . 2009-07-09 20:50 90112 ----a-r- c:\windows\system32\IS3Svc5.dll
2009-07-09 20:47 . 2009-07-09 20:47 724992 ----a-r- c:\windows\system32\IS3Base5.dll
2009-07-08 18:44 . 2009-07-08 18:44 214024 ----a-w- c:\windows\system32\drivers\mfehidk.sys
2009-07-03 17:09 . 2001-08-23 12:00 915456 ----a-w- c:\windows\system32\wininet.dll
.
------- Sigcheck -------
[7] 2008-04-14 . 6D4FEB43EE538FC5428CC7F0565AA656 . 56320 . . [5.1.2600.5512] . . c:\windows\ServicePackFiles\i386\eventlog.dll
[7] 2004-08-04 . 82B24CB70E5944E6E34662205A2A5B78 . 55808 . . [5.1.2600.2180] . . c:\windows\$NtServicePackUninstall$\eventlog.dll
c:\windows\system32\eventlog.dll ... is missing !!
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"MoneyAgent"="c:\program files\Microsoft Money\System\mnyexpr.exe" [2002-07-17 200767]
"BgMonitor_{79662E04-7C6C-4d9f-84C7-88D8A56B10AA}"="c:\program files\Common Files\Ahead\Lib\NMBgMonitor.exe" [2006-11-17 139264]
"DW6"="c:\program files\The Weather Channel FW\Desktop\DesktopWeather.exe" [2009-02-11 801904]
"swg"="c:\program files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe" [2009-01-21 39408]
"Google Update"="c:\documents and settings\Dennis\Local Settings\Application Data\Google\Update\GoogleUpdate.exe" [2009-03-15 133104]
"ctfmon.exe"="c:\windows\system32\ctfmon.exe" [2008-04-14 15360]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"zBrowser Launcher"="c:\program files\Logitech\iTouch\iTouch.exe" [2004-03-18 892928]
"Picasa Media Detector"="c:\program files\Picasa2\PicasaMediaDetector.exe" [2005-10-28 335872]
"RemoteControl"="c:\program files\CyberLink\PowerDVD\PDVDServ.exe" [2005-12-08 30208]
"LanguageShortcut"="c:\program files\CyberLink\PowerDVD\Language\Language.exe" [2006-04-13 49152]
"NeroFilterCheck"="c:\program files\Common Files\Ahead\Lib\NeroCheck.exe" [2006-01-12 155648]
"WatchDog"="c:\program files\mobile PhoneTools\WatchDog.exe" [2004-08-14 36864]
"dvd43"="c:\program files\dvd43\dvd43_tray.exe" [2007-11-20 731136]
"Mirabilis ICQ"="c:\progra~1\ICQ\ICQNet.exe" [2003-10-14 38984]
"AppleSyncNotifier"="c:\program files\Common Files\Apple\Mobile Device Support\bin\AppleSyncNotifier.exe" [2009-08-13 177440]
"WinampAgent"="c:\program files\Winamp\winampa.exe" [2008-08-03 36352]
"MioNet"="c:\program files\MioNet\MioNetLauncher.exe" [2008-01-14 32768]
"WD Anywhere Backup"="c:\program files\WD\WD Anywhere Backup\MemeoLauncher2.exe" [2009-04-17 197856]
"SunJavaUpdateSched"="c:\program files\Java\jre6\bin\jusched.exe" [2009-07-25 149280]
"QuickTime Task"="c:\program files\QuickTime\qttask.exe" [2009-09-05 417792]
"iTunesHelper"="c:\program files\iTunes\iTunesHelper.exe" [2009-09-09 305440]
"Malwarebytes Anti-Malware (reboot)"="c:\program files\Malwarebytes' Anti-Malware\mbam.exe" [2009-09-10 1312080]
"mcagent_exe"="c:\program files\McAfee.com\Agent\mcagent.exe" [2009-07-10 645328]
"Logitech Utility"="Logi_MwX.Exe" - c:\windows\LOGI_MWX.EXE [2003-12-17 19968]
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Run]
"DWQueuedReporting"="c:\progra~1\COMMON~1\MICROS~1\DW\dwtrig20.exe" [2007-03-13 39264]
c:\documents and settings\All Users\Start Menu\Programs\Startup\
Adobe Reader Speed Launch.lnk - c:\program files\Adobe\Acrobat 7.0\Reader\reader_sl.exe [2008-4-23 29696]
HP Digital Imaging Monitor.lnk - c:\program files\HP\Digital Imaging\bin\hpqtra08.exe [2005-5-11 282624]
HP Image Zone Fast Start.lnk - c:\program files\HP\Digital Imaging\bin\hpqthb08.exe [2005-5-12 73728]
Microsoft Office.lnk - c:\program files\Microsoft Office\Office10\OSA.EXE [2001-2-13 83360]
Windows Search.lnk - c:\program files\Windows Desktop Search\WindowsSearch.exe [2008-5-26 123904]
[HKEY_USERS\.default\software\microsoft\windows\currentversion\policies\explorer]
"NoSetActiveDesktop"= 1 (0x1)
"NoActiveDesktopChanges"= 1 (0x1)
[hkey_local_machine\software\microsoft\windows\currentversion\explorer\ShellExecuteHooks]
"{56F9679E-7826-4C84-81F3-532071A8BCC5}"= "c:\program files\Windows Desktop Search\MSNLNamespaceMgr.dll" [2009-05-25 304128]
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\drivers32]
"aux"=wdmaud.sys
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\mcmscsvc]
@=""
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\MCODS]
@=""
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\McAfeeAntiVirus]
"DisableMonitoring"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\McAfeeFirewall]
"DisableMonitoring"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile]
"EnableFirewall"= 0 (0x0)
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"c:\\Program Files\\ICQ\\Icq.exe"=
"c:\\Program Files\\K-Lite\\kazaa.core"=
"c:\\Program Files\\LimeWire\\LimeWire.exe"=
"c:\\WINDOWS\\system32\\spoolsv.exe"=
"c:\\Program Files\\Common Files\\Ahead\\Nero Web\\SetupX.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpqtra08.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpqste08.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpofxm08.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hposfx08.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hposid01.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpqscnvw.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpqkygrp.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpqCopy.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpfccopy.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpzwiz01.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\Unload\\HpqPhUnl.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\Unload\\HpqDIA.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpoews01.exe"=
"c:\\Program Files\\Azureus\\Azureus.exe"=
"%windir%\\Network Diagnostic\\xpnetdiag.exe"=
"c:\\Program Files\\MioNet\\jvm\\bin\\MioNet.exe"=
"c:\\Program Files\\MioNet\\MioNetManager.exe"=
"c:\\Program Files\\Bonjour\\mDNSResponder.exe"=
"c:\\Program Files\\Motorola\\Software Update\\msu.exe"=
"c:\\Program Files\\Common Files\\McAfee\\MNA\\McNASvc.exe"=
"c:\\Program Files\\iTunes\\iTunes.exe"=
"c:\\Documents and Settings\\Dennis\\Local Settings\\Application Data\\Google\\Chrome\\Application\\chrome.exe"=
"c:\\Program Files\\McAfee\\VirusScan\\mcvsmap.exe"=
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"1700:TCP"= 1700:TCP:MioNet Remote Drive Access 0
"1701:TCP"= 1701:TCP:MioNet Remote Drive Access 1
"1702:TCP"= 1702:TCP:MioNet Remote Drive Access 2
"1703:TCP"= 1703:TCP:MioNet Remote Drive Access 3
"1704:TCP"= 1704:TCP:MioNet Remote Drive Access 4
"1705:TCP"= 1705:TCP:MioNet Remote Drive Access 5
"1706:TCP"= 1706:TCP:MioNet Remote Drive Access 6
"1707:TCP"= 1707:TCP:MioNet Remote Drive Access 7
"1708:TCP"= 1708:TCP:MioNet Remote Drive Access 8
"1709:TCP"= 1709:TCP:MioNet Remote Drive Access 9
"1641:TCP"= 1641:TCP:MioNet Remote Drive Verification
"1647:TCP"= 1647:TCP:MioNet Storage Device Configuration
"5432:UDP"= 5432:UDP:MioNet Storage Device Discovery
R0 si3112r;Silicon Image SiI 3112 SATARaid Controller;c:\windows\system32\drivers\SI3112r.sys [9/10/2006 11:05 AM 116264]
R0 SiWinAcc;SiWinAcc;c:\windows\system32\drivers\SiWinAcc.sys [9/10/2006 11:05 AM 19240]
R0 szkg5;szkg;c:\windows\system32\drivers\SZKG.sys [5/12/2009 2:13 PM 61328]
R2 MioNet;MioNet;c:\program files\MioNet\MioNetManager.exe [1/14/2008 3:14 PM 139264]
R3 LCcfltr;Logitech USB Filter Driver;c:\windows\system32\drivers\LCcfltr.sys [9/13/2006 11:36 PM 14095]
S2 MemeoBackgroundService;MemeoBackgroundService;c:\program files\WD\WD Anywhere Backup\MemeoBackgroundService.exe [4/17/2009 12:51 PM 25824]
S3 lgatbus;LG USB Composite Device driver (WDM);c:\windows\system32\drivers\lgatbus.sys [3/16/2009 6:10 PM 43024]
S3 lgatmdm;LG CDMA USB Modem Drivers;c:\windows\system32\drivers\lgatmdm.sys [3/16/2009 6:11 PM 77104]
S3 lgatserd;LG CDMA USB Modem Diagnostic Serial Port Drivers (WDM);c:\windows\system32\drivers\lgatserd.sys [3/16/2009 6:11 PM 60816]
S3 motccgp;Motorola USB Composite Device Driver;c:\windows\system32\drivers\motccgp.sys [3/18/2009 8:55 PM 18688]
S3 motccgpfl;MotCcgpFlService;c:\windows\system32\drivers\motccgpfl.sys [3/18/2009 8:55 PM 8320]
S3 MotDev;Motorola Inc. USB Device;c:\windows\system32\drivers\motodrv.sys [3/18/2009 8:55 PM 42112]
S3 Sus2pl;Susteen Universal Cable II;c:\windows\system32\drivers\sus2pl.sys [3/31/2004 3:33 PM 43392]
[HKEY_LOCAL_MACHINE\software\microsoft\active setup\installed components\>{60B49E34-C7CC-11D0-8953-00A0C90347FF}]
"c:\windows\system32\rundll32.exe" "c:\windows\system32\iedkcs32.dll",BrandIEActiveSetup SIGNUP
.
Contents of the 'Scheduled Tasks' folder
2009-09-24 c:\windows\Tasks\AppleSoftwareUpdate.job
- c:\program files\Apple Software Update\SoftwareUpdate.exe [2008-07-30 17:34]
2009-09-24 c:\windows\Tasks\GoogleUpdateTaskUserS-1-5-21-682003330-1563985344-839522115-1003Core.job
- c:\documents and settings\Dennis\Local Settings\Application Data\Google\Update\GoogleUpdate.exe [2009-03-15 17:14]
2009-09-24 c:\windows\Tasks\GoogleUpdateTaskUserS-1-5-21-682003330-1563985344-839522115-1003UA.job
- c:\documents and settings\Dennis\Local Settings\Application Data\Google\Update\GoogleUpdate.exe [2009-03-15 17:14]
2009-09-27 c:\windows\Tasks\McDefragTask.job
- c:\progra~1\mcafee\mqc\QcConsol.exe [2009-09-27 02:26]
2009-09-27 c:\windows\Tasks\McQcTask.job
- c:\progra~1\mcafee\mqc\QcConsol.exe [2009-09-27 02:26]
2009-09-24 c:\windows\Tasks\SDMsgUpdate (TE).job
- c:\progra~1\SMARTD~1\Messages\SDNotify.exe [2009-06-12 14:29]
.
.
------- Supplementary Scan -------
.
uStart Page = hxxp://www.google.com/ig
uInternet Settings,ProxyOverride = *.local
uSearchURL,(Default) = hxxp://www.google.com/keyword/%s
IE: E&xport to Microsoft Excel - c:\progra~1\MICROS~2\Office10\EXCEL.EXE/3000
.
- - - - ORPHANS REMOVED - - - -
WebBrowser-{604BC32A-9680-40D1-9AC6-E06B23A1BA4C} - (no file)
WebBrowser-{D4027C7F-154A-4066-A1AD-4243D8127440} - (no file)
HKLM-Run-NWEReboot - (no file)
SharedTaskScheduler-{511e8a45-6d1a-4308-b77a-5b1b46e84736} - c:\windows\system32\kowogepu.dll
SSODL-bepedubor-{511e8a45-6d1a-4308-b77a-5b1b46e84736} - c:\windows\system32\kowogepu.dll
Notify-NavLogon - (no file)
AddRemove-{7B63B2922B174135AFC0E1377DD81EC2} - c:\program files\DivX\DivXCodecUninstall.exe
AddRemove-{8ADFC4160D694100B5B8A22DE9DCABD9} - c:\program files\DivX\DivXPlayerUninstall.exe
AddRemove-{B7050CBDB2504B34BC2A9CA0A692CC29} - c:\program files\DivX\DivXWebPlayerUninstall.exe
**************************************************************************
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2009-09-27 14:18
Windows 5.1.2600 Service Pack 3 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
c:\docume~1\Dennis\LOCALS~1\Temp\16.tmp 0 bytes
c:\documents and settings\Dennis\Application Data\WD\WD Anywhere Backup\instances\654D5BBC-7376-45D4-9A09-97AD1B4AB98B\manifest.db3-journal
scan completed successfully
hidden files: 2
**************************************************************************
.
--------------------- DLLs Loaded Under Running Processes ---------------------
- - - - - - - > 'winlogon.exe'(1272)
c:\windows\system32\Ati2evxx.dll
- - - - - - - > 'explorer.exe'(7340)
c:\windows\system32\WININET.dll
c:\program files\Logitech\MouseWare\System\LgWndHk.dll
c:\program files\Logitech\iTouch\iTchHk.dll
c:\program files\Common Files\Logitech\Scrolling\LgMsgHk.dll
c:\progra~1\WINDOW~3\wmpband.dll
c:\program files\Windows Desktop Search\deskbar.dll
c:\program files\Windows Desktop Search\en-us\dbres.dll.mui
c:\program files\Windows Desktop Search\dbres.dll
c:\program files\Windows Desktop Search\wordwheel.dll
c:\program files\Windows Desktop Search\en-us\msnlExtRes.dll.mui
c:\program files\Windows Desktop Search\msnlExtRes.dll
c:\windows\system32\ieframe.dll
c:\windows\system32\webcheck.dll
c:\windows\system32\WPDShServiceObj.dll
c:\program files\Microsoft Virtual PC\VPCShExH.DLL
c:\windows\system32\PortableDeviceTypes.dll
c:\windows\system32\PortableDeviceApi.dll
.
------------------------ Other Running Processes ------------------------
.
c:\windows\system32\ati2evxx.exe
c:\windows\system32\ati2evxx.exe
c:\program files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
c:\program files\Symantec\LiveUpdate\AluSchedulerSvc.exe
c:\program files\Bonjour\mDNSResponder.exe
c:\windows\system32\CTSVCCDA.EXE
c:\program files\Java\jre6\bin\jqs.exe
c:\progra~1\McAfee\MSC\mcmscsvc.exe
c:\progra~1\COMMON~1\McAfee\MNA\McNASvc.exe
c:\progra~1\COMMON~1\McAfee\McProxy\McProxy.exe
c:\progra~1\McAfee\VIRUSS~1\Mcshield.exe
c:\program files\McAfee\MPF\MpfSrv.exe
c:\program files\MioNet\jvm\bin\MioNet.exe
c:\windows\system32\HPZipm12.exe
c:\program files\CyberLink\Shared files\RichVideo.exe
c:\windows\system32\searchindexer.exe
c:\progra~1\McAfee.com\Agent\mcagent.exe
c:\program files\Logitech\MouseWare\system\EM_EXEC.EXE
c:\progra~1\ICQ\Icq.exe
c:\program files\Common Files\Ahead\Lib\NMIndexStoreSvr.exe
c:\progra~1\McAfee\VIRUSS~1\mcsysmon.exe
c:\program files\MioNet\jvm\bin\MioNet.exe
c:\program files\HP\Digital Imaging\bin\hpqimzone.exe
c:\program files\iPod\bin\iPodService.exe
c:\program files\WD\WD Anywhere Backup\MemeoBackup.exe
c:\windows\system32\searchprotocolhost.exe
c:\windows\system32\searchfilterhost.exe
.
**************************************************************************
.
Completion time: 2009-09-27 14:33 - machine was rebooted
ComboFix-quarantined-files.txt 2009-09-27 19:32
Pre-Run: 33,507,909,632 bytes free
Post-Run: 33,825,972,224 bytes free
WindowsXP-KB310994-SP2-Pro-BootDisk-ENU.exe
[boot loader]
timeout=2
default=multi(0)disk(0)rdisk(1)partition(1)\WINDOWS
[operating systems]
f:\cmdcons\BOOTSECT.DAT="Microsoft Windows Recovery Console" /cmdcons
multi(0)disk(0)rdisk(1)partition(1)\WINDOWS="Microsoft Windows XP Professional" /fastdetect
Current=2 Default=2 Failed=1 LastKnownGood=4 Sets=1,2,3,4
448 --- E O F --- 2009-09-27 04:32
#9
![[Resolved] Computer Hijacked: post #9](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 27 September 2009 - 02:15 PM
Please do the following:
- Very Important! Temporarily disable your anti-virus, script blocking and any anti-malware real-time protection before following the steps below.
- They can interfere with ComboFix or remove some of its embedded files which may cause "unpredictable results".
Here's how to do that:
Click Start > Run type Notepad click OK.
This will open an empty notepad file:
Copy all the text inside of the code box - Press Ctrl+C (or right click on the highlighted section and choose 'copy')
http://forums.whatthetech.com/Computer_Hijacked_t107168.html&view=findpost&p=599204#entry599204 Collect:: c:\windows\system32\nigun.dat c:\windows\system32\fozyreg.dat c:\program files\Common Files\wolydycud.dat c:\windows\jemutogeh.dat c:\windows\system32\0fb49.dll c:\windows\system32\0fb49.sys c:\program files\Common Files\naneg.dat c:\windows\ijyjodiw.com c:\windows\tuxawuni.com c:\documents and settings\All Users\Application Data\femapoh.dat c:\documents and settings\All Users\Application Data\ocuwyp.dat c:\program files\Common Files\yfanu.lib FCopy:: c:\windows\ServicePackFiles\i386\eventlog.dll | c:\windows\system32\eventlog.dll
Now paste the copied text into the open notepad - press CTRL+V (or right click and choose 'paste')
Save this file to your desktop, Save this as "CFScript"
Here's how to do that:
1.Click File;
2.Click Save As... Change the directory to your desktop;
3.Change the Save as type to "All Files";
4.Type in the file name: CFScript
5.Click Save ...

- Referring to the screenshot above, drag CFScript.txt into ComboFix.exe.
- ComboFix will now run a scan on your system. It may reboot your system when it finishes. This is normal.
- When finished, it shall produce a log for you.
- Copy and paste the contents of the log in your next reply.
CAUTION: Do not mouse-click ComboFix's window while it is running. That may cause it to stall.
**Note**
When CF finishes running, the ComboFix log will open along with a message box--do not be alarmed. With the above script, ComboFix will capture files to submit for analysis.
- Ensure you are connected to the internet and click OK on the message box.
NEXT
- Please open your MalwareBytes AntiMalware Program
- Click the Update Tab and search for updates
- If an update is found, it will download and install the latest version.
- Once the program has loaded, select "Perform Quick Scan", then click Scan.
- The scan may take some time to finish, so please be patient.
- When the scan is complete, click OK, then Show Results to view the results.
- Make sure that everything is checked, and click Remove Selected. <-- very important
- When disinfection is completed, a log will open in Notepad and you may be prompted to Restart. (See Extra Note)
- The log is automatically saved by MBAM and can be viewed by clicking the Logs tab in MBAM.
- Copy&Paste the entire report in your next reply.
Extra Note:If MBAM encounters a file that is difficult to remove, you will be presented with 1 of 2 prompts, click OK to either and let MBAM proceed with the disinfection process, if asked to restart the computer, please do so immediately.
NEXT
Run an on-line scan with Kaspersky
Using Internet Explorer or Firefox, visit Kaspersky On-line Scanner
1. Click Accept, when prompted to download and install the program files and database of malware definitions.
2. To optimize scanning time and produce a more sensible report for review:
- Close any open programs
- Turn off the real time scanner of any existing antivirus program while performing the online scan
The program will then begin downloading and installing and will also update the database.
Please be patient as this can take several minutes.
- Once the update is complete, click on My Computer under the green Scan bar to the left to start the scan.
- Once the scan is complete, it will display if your system has been infected. It does not provide an option to clean/disinfect. We only require a report from it.
- Do NOT be alarmed by what you see in the report. Many of the finds have likely been quarantined.
- Click View scan report at the bottom.
- Click the Save as Text button to save the file to your desktop so that you may post it in your next reply
Microsoft MVP 2010, 2011, 2012, 2013, 2014, 2015
#10
![[Resolved] Computer Hijacked: post #10](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 28 September 2009 - 06:21 PM
Microsoft Windows XP Professional 5.1.2600.3.1252.1.1033.18.1535.798 [GMT -5:00]
Running from: c:\documents and settings\Dennis\Desktop\Combo-Fix.exe
Command switches used :: c:\documents and settings\Dennis\Desktop\CFScript.txt
AV: McAfee VirusScan *On-access scanning disabled* (Updated) {84B5EE75-6421-4CDE-A33A-DD43BA9FAD83}
FW: McAfee Personal Firewall *disabled* {94894B63-8C7F-4050-BDA4-813CA00DA3E8}
file zipped: c:\documents and settings\All Users\Application Data\femapoh.dat
file zipped: c:\documents and settings\All Users\Application Data\ocuwyp.dat
file zipped: c:\program files\Common Files\naneg.dat
file zipped: c:\program files\Common Files\wolydycud.dat
file zipped: c:\program files\Common Files\yfanu.lib
file zipped: c:\windows\ijyjodiw.com
file zipped: c:\windows\jemutogeh.dat
file zipped: c:\windows\system32\0fb49.dll
file zipped: c:\windows\system32\0fb49.sys
file zipped: c:\windows\system32\fozyreg.dat
file zipped: c:\windows\system32\nigun.dat
file zipped: c:\windows\tuxawuni.com
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
c:\documents and settings\All Users\Application Data\femapoh.dat
c:\documents and settings\All Users\Application Data\ocuwyp.dat
c:\program files\Common Files\naneg.dat
c:\program files\Common Files\wolydycud.dat
c:\program files\Common Files\yfanu.lib
c:\windows\ijyjodiw.com
c:\windows\jemutogeh.dat
c:\windows\system32\0fb49.dll
c:\windows\system32\0fb49.sys
c:\windows\system32\fozyreg.dat
c:\windows\system32\nigun.dat
c:\windows\tuxawuni.com
.
--------------- FCopy ---------------
c:\windows\ServicePackFiles\i386\eventlog.dll --> c:\windows\system32\eventlog.dll
.
((((((((((((((((((((((((( Files Created from 2009-08-27 to 2009-09-27 )))))))))))))))))))))))))))))))
.
2009-09-27 20:28 . 2008-04-14 00:11 56320 -c--a-w- c:\windows\system32\dllcache\eventlog.dll
2009-09-27 20:28 . 2008-04-14 00:11 56320 ----a-w- c:\windows\system32\eventlog.dll
2009-09-27 19:11 . 2008-04-14 00:12 50176 -c--a-w- c:\windows\system32\dllcache\proquota.exe
2009-09-27 19:11 . 2008-04-14 00:12 50176 ----a-w- c:\windows\system32\proquota.exe
2009-09-27 17:56 . 2009-09-27 17:56 -------- d-sh--w- c:\documents and settings\Dennis\IECompatCache
2009-09-27 17:54 . 2009-09-27 17:54 -------- d-sh--w- c:\documents and settings\Dennis\PrivacIE
2009-09-27 17:31 . 2008-04-13 19:18 52480 -c--a-w- c:\windows\system32\dllcache\i8042prt.sys
2009-09-27 17:31 . 2008-04-13 19:18 52480 ----a-w- c:\windows\system32\drivers\i8042prt.sys
2009-09-27 17:28 . 2009-09-27 17:28 -------- d-sh--w- c:\documents and settings\LocalService\IETldCache
2009-09-27 17:27 . 2009-09-27 17:27 -------- d-sh--w- c:\documents and settings\Dennis\IETldCache
2009-09-27 16:58 . 2009-09-27 16:58 -------- d-----w- C:\$dpx$.tmp
2009-09-27 04:32 . 2009-08-07 08:48 100352 -c----w- c:\windows\system32\dllcache\iecompat.dll
2009-09-27 04:32 . 2009-09-27 04:32 -------- d-----w- c:\windows\ie8updates
2009-09-27 04:31 . 2009-07-03 17:09 12800 -c----w- c:\windows\system32\dllcache\xpshims.dll
2009-09-27 04:31 . 2009-07-03 17:09 246272 -c----w- c:\windows\system32\dllcache\ieproxy.dll
2009-09-27 04:29 . 2009-09-27 04:31 -------- dc-h--w- c:\windows\ie8
2009-09-27 00:44 . 2009-07-08 18:44 79816 ----a-w- c:\windows\system32\drivers\mfeavfk.sys
2009-09-27 00:44 . 2009-07-08 18:44 40552 ----a-w- c:\windows\system32\drivers\mfesmfk.sys
2009-09-27 00:44 . 2009-07-08 18:44 35272 ----a-w- c:\windows\system32\drivers\mfebopk.sys
2009-09-27 00:44 . 2009-07-16 17:32 120136 ----a-w- c:\windows\system32\drivers\Mpfp.sys
2009-09-27 00:43 . 2009-09-27 00:44 -------- d-----w- c:\program files\Common Files\McAfee
2009-09-27 00:43 . 2009-09-27 00:43 -------- d-----w- c:\program files\McAfee.com
2009-09-27 00:43 . 2009-09-27 17:43 -------- d-----w- c:\program files\McAfee
2009-09-27 00:39 . 2009-07-08 18:43 34248 ----a-w- c:\windows\system32\drivers\mferkdk.sys
2009-09-24 01:30 . 2009-09-24 01:30 -------- d-----w- c:\program files\Trend Micro
2009-09-24 00:32 . 2009-09-24 00:32 -------- d-----w- c:\documents and settings\All Users\Application Data\SITEguard
2009-09-24 00:32 . 2009-09-24 00:32 -------- d-----w- c:\program files\STOPzilla!
2009-09-24 00:32 . 2009-09-24 00:32 -------- d-----w- c:\program files\Common Files\iS3
2009-09-24 00:32 . 2009-09-24 00:33 -------- d-----w- c:\documents and settings\All Users\Application Data\STOPzilla!
2009-09-24 00:11 . 2009-09-10 19:54 38224 ----a-w- c:\windows\system32\drivers\mbamswissarmy.sys
2009-09-24 00:11 . 2009-09-26 04:11 -------- d-----w- c:\program files\Malwarebytes' Anti-Malware
2009-09-24 00:11 . 2009-09-10 19:53 19160 ----a-w- c:\windows\system32\drivers\mbam.sys
2009-09-23 04:28 . 2009-09-23 04:28 -------- d-----w- c:\documents and settings\Dennis\Application Data\Malwarebytes
2009-09-23 04:28 . 2009-09-23 04:28 -------- d-----w- c:\documents and settings\All Users\Application Data\Malwarebytes
2009-09-22 02:51 . 2009-09-22 02:51 93632 ----a-w- c:\documents and settings\LocalService\Local Settings\Application Data\FontCache3.0.0.0.dat
2009-09-22 02:49 . 2009-09-22 02:49 -------- d-----w- c:\documents and settings\Dennis\Local Settings\Application Data\Apple_Inc
2009-09-17 02:06 . 2009-09-17 02:06 -------- d-----w- c:\program files\iPhone Configuration Utility
2009-09-17 02:01 . 2009-09-17 02:01 -------- d-----w- c:\program files\iPod
2009-09-17 02:00 . 2009-09-17 02:03 -------- d-----w- c:\program files\iTunes
2009-09-17 02:00 . 2009-09-17 02:03 -------- d-----w- c:\documents and settings\All Users\Application Data\{755AC846-7372-4AC8-8550-C52491DAA8BD}
2009-09-10 01:55 . 2009-06-21 21:44 153088 -c----w- c:\windows\system32\dllcache\triedit.dll
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2009-09-27 19:23 . 2008-12-25 23:21 -------- d-----w- c:\documents and settings\Dennis\Application Data\MioNet
2009-09-27 00:57 . 2009-07-26 13:48 -------- d-----w- c:\documents and settings\All Users\Application Data\McAfee
2009-09-27 00:46 . 2008-12-25 23:20 -------- d-----w- c:\program files\MioNet
2009-09-26 04:04 . 2006-12-12 04:35 -------- d-----w- c:\program files\Windows Defender
2009-09-26 04:03 . 2008-02-29 14:23 -------- d-----w- c:\program files\ICQ
2009-09-17 02:35 . 2006-09-15 03:27 -------- d-----w- c:\documents and settings\Dennis\Application Data\Apple Computer
2009-09-17 02:01 . 2007-10-18 01:03 -------- d-----w- c:\program files\Common Files\Apple
2009-09-17 01:56 . 2006-09-15 03:27 -------- d-----w- c:\program files\QuickTime
2009-09-17 00:47 . 2006-11-13 02:25 -------- d-----w- c:\program files\Java
2009-09-05 20:16 . 2007-12-27 03:18 -------- d-----w- c:\documents and settings\Dennis\Application Data\Azureus
2009-08-29 00:42 . 2008-09-11 01:23 2065696 ----a-w- c:\windows\system32\usbaaplrc.dll
2009-08-29 00:42 . 2007-10-18 01:03 40448 ----a-w- c:\windows\system32\drivers\usbaapl.sys
2009-08-26 14:09 . 2009-08-25 18:49 -------- d-----w- c:\program files\Total 3D Home
2009-08-25 20:43 . 2009-08-25 20:43 -------- d-----w- c:\documents and settings\Dennis\Application Data\Individual Software
2009-08-25 19:30 . 2009-08-25 18:49 -------- d-----w- c:\program files\Common Files\Individual Software
2009-08-25 19:28 . 2009-08-25 19:28 -------- d-----w- c:\documents and settings\All Users\Application Data\Individual Software
2009-08-20 22:22 . 2006-11-29 01:56 -------- d-----w- c:\documents and settings\All Users\Application Data\SnapStream
2009-08-20 22:21 . 2006-11-29 01:50 -------- d-----w- c:\program files\SnapStream Media
2009-08-15 08:29 . 2006-09-14 04:30 33504 ----a-w- c:\documents and settings\Dennis\Local Settings\Application Data\GDIPFONTCACHEV1.DAT
2009-08-15 08:10 . 2009-08-15 08:10 -------- d-----w- c:\program files\MSBuild
2009-08-15 08:10 . 2009-08-15 08:10 -------- d-----w- c:\program files\Reference Assemblies
2009-08-08 02:37 . 2007-12-27 03:17 -------- d-----w- c:\program files\Azureus
2009-08-05 09:01 . 2001-08-23 12:00 204800 ----a-w- c:\windows\system32\mswebdvd.dll
2009-07-25 10:23 . 2009-02-22 17:29 411368 ----a-w- c:\windows\system32\deploytk.dll
2009-07-20 19:57 . 2009-07-20 19:57 17408 ----a-r- c:\windows\system32\SZIO5.dll
2009-07-20 19:56 . 2009-07-20 19:56 311296 ----a-r- c:\windows\system32\SZBase5.dll
2009-07-20 19:56 . 2009-07-20 19:56 540672 ----a-r- c:\windows\system32\SZComp5.dll
2009-07-17 19:01 . 2001-08-23 12:00 58880 ----a-w- c:\windows\system32\atl.dll
2009-07-14 04:43 . 2006-09-14 04:19 286208 ----a-w- c:\windows\system32\wmpdxm.dll
2009-07-09 20:52 . 2009-07-09 20:52 126976 ----a-r- c:\windows\system32\IS3HTUI5.dll
2009-07-09 20:52 . 2009-07-09 20:52 393216 ----a-r- c:\windows\system32\IS3DBA5.dll
2009-07-09 20:51 . 2009-07-09 20:51 385024 ----a-r- c:\windows\system32\IS3UI5.dll
2009-07-09 20:51 . 2009-07-09 20:51 61440 ----a-r- c:\windows\system32\IS3Hks5.dll
2009-07-09 20:51 . 2009-07-09 20:51 23040 ----a-r- c:\windows\system32\IS3XDat5.dll
2009-07-09 20:50 . 2009-07-09 20:50 225280 ----a-r- c:\windows\system32\IS3Win325.dll
2009-07-09 20:50 . 2009-07-09 20:50 94208 ----a-r- c:\windows\system32\IS3Inet5.dll
2009-07-09 20:50 . 2009-07-09 20:50 90112 ----a-r- c:\windows\system32\IS3Svc5.dll
2009-07-09 20:47 . 2009-07-09 20:47 724992 ----a-r- c:\windows\system32\IS3Base5.dll
2009-07-08 18:44 . 2009-07-08 18:44 214024 ----a-w- c:\windows\system32\drivers\mfehidk.sys
2009-07-03 17:09 . 2001-08-23 12:00 915456 ------w- c:\windows\system32\wininet.dll
.
((((((((((((((((((((((((((((( SnapShot@2009-09-27_19.18.45 )))))))))))))))))))))))))))))))))))))))))
.
- 2001-08-23 12:00 . 2009-09-27 17:49 78772 c:\windows\system32\perfc009.dat
+ 2001-08-23 12:00 . 2009-09-27 19:23 78772 c:\windows\system32\perfc009.dat
+ 2001-08-23 12:00 . 2009-09-27 19:23 463404 c:\windows\system32\perfh009.dat
- 2001-08-23 12:00 . 2009-09-27 17:49 463404 c:\windows\system32\perfh009.dat
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"MoneyAgent"="c:\program files\Microsoft Money\System\mnyexpr.exe" [2002-07-17 200767]
"BgMonitor_{79662E04-7C6C-4d9f-84C7-88D8A56B10AA}"="c:\program files\Common Files\Ahead\Lib\NMBgMonitor.exe" [2006-11-17 139264]
"DW6"="c:\program files\The Weather Channel FW\Desktop\DesktopWeather.exe" [2009-02-11 801904]
"swg"="c:\program files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe" [2009-01-21 39408]
"Google Update"="c:\documents and settings\Dennis\Local Settings\Application Data\Google\Update\GoogleUpdate.exe" [2009-03-15 133104]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"zBrowser Launcher"="c:\program files\Logitech\iTouch\iTouch.exe" [2004-03-18 892928]
"Picasa Media Detector"="c:\program files\Picasa2\PicasaMediaDetector.exe" [2005-10-28 335872]
"RemoteControl"="c:\program files\CyberLink\PowerDVD\PDVDServ.exe" [2005-12-08 30208]
"LanguageShortcut"="c:\program files\CyberLink\PowerDVD\Language\Language.exe" [2006-04-13 49152]
"NeroFilterCheck"="c:\program files\Common Files\Ahead\Lib\NeroCheck.exe" [2006-01-12 155648]
"WatchDog"="c:\program files\mobile PhoneTools\WatchDog.exe" [2004-08-14 36864]
"dvd43"="c:\program files\dvd43\dvd43_tray.exe" [2007-11-20 731136]
"Mirabilis ICQ"="c:\progra~1\ICQ\ICQNet.exe" [2003-10-14 38984]
"AppleSyncNotifier"="c:\program files\Common Files\Apple\Mobile Device Support\bin\AppleSyncNotifier.exe" [2009-08-13 177440]
"WinampAgent"="c:\program files\Winamp\winampa.exe" [2008-08-03 36352]
"MioNet"="c:\program files\MioNet\MioNetLauncher.exe" [2008-01-14 32768]
"WD Anywhere Backup"="c:\program files\WD\WD Anywhere Backup\MemeoLauncher2.exe" [2009-04-17 197856]
"SunJavaUpdateSched"="c:\program files\Java\jre6\bin\jusched.exe" [2009-07-25 149280]
"QuickTime Task"="c:\program files\QuickTime\qttask.exe" [2009-09-05 417792]
"iTunesHelper"="c:\program files\iTunes\iTunesHelper.exe" [2009-09-09 305440]
"Malwarebytes Anti-Malware (reboot)"="c:\program files\Malwarebytes' Anti-Malware\mbam.exe" [2009-09-10 1312080]
"mcagent_exe"="c:\program files\McAfee.com\Agent\mcagent.exe" [2009-07-10 645328]
"Logitech Utility"="Logi_MwX.Exe" - c:\windows\LOGI_MWX.EXE [2003-12-17 19968]
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Run]
"DWQueuedReporting"="c:\progra~1\COMMON~1\MICROS~1\DW\dwtrig20.exe" [2007-03-13 39264]
c:\documents and settings\All Users\Start Menu\Programs\Startup\
Adobe Reader Speed Launch.lnk - c:\program files\Adobe\Acrobat 7.0\Reader\reader_sl.exe [2008-4-23 29696]
HP Digital Imaging Monitor.lnk - c:\program files\HP\Digital Imaging\bin\hpqtra08.exe [2005-5-11 282624]
HP Image Zone Fast Start.lnk - c:\program files\HP\Digital Imaging\bin\hpqthb08.exe [2005-5-12 73728]
Microsoft Office.lnk - c:\program files\Microsoft Office\Office10\OSA.EXE [2001-2-13 83360]
Windows Search.lnk - c:\program files\Windows Desktop Search\WindowsSearch.exe [2008-5-26 123904]
[HKEY_USERS\.default\software\microsoft\windows\currentversion\policies\explorer]
"NoSetActiveDesktop"= 1 (0x1)
"NoActiveDesktopChanges"= 1 (0x1)
[hkey_local_machine\software\microsoft\windows\currentversion\explorer\ShellExecuteHooks]
"{56F9679E-7826-4C84-81F3-532071A8BCC5}"= "c:\program files\Windows Desktop Search\MSNLNamespaceMgr.dll" [2009-05-25 304128]
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\drivers32]
"aux"=wdmaud.sys
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\mcmscsvc]
@=""
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\MCODS]
@=""
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\McAfeeAntiVirus]
"DisableMonitoring"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\McAfeeFirewall]
"DisableMonitoring"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile]
"EnableFirewall"= 0 (0x0)
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"c:\\Program Files\\ICQ\\Icq.exe"=
"c:\\Program Files\\K-Lite\\kazaa.core"=
"c:\\Program Files\\LimeWire\\LimeWire.exe"=
"c:\\WINDOWS\\system32\\spoolsv.exe"=
"c:\\Program Files\\Common Files\\Ahead\\Nero Web\\SetupX.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpqtra08.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpqste08.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpofxm08.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hposfx08.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hposid01.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpqscnvw.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpqkygrp.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpqCopy.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpfccopy.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpzwiz01.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\Unload\\HpqPhUnl.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\Unload\\HpqDIA.exe"=
"c:\\Program Files\\HP\\Digital Imaging\\bin\\hpoews01.exe"=
"c:\\Program Files\\Azureus\\Azureus.exe"=
"%windir%\\Network Diagnostic\\xpnetdiag.exe"=
"c:\\Program Files\\MioNet\\jvm\\bin\\MioNet.exe"=
"c:\\Program Files\\MioNet\\MioNetManager.exe"=
"c:\\Program Files\\Bonjour\\mDNSResponder.exe"=
"c:\\Program Files\\Motorola\\Software Update\\msu.exe"=
"c:\\Program Files\\Common Files\\McAfee\\MNA\\McNASvc.exe"=
"c:\\Program Files\\iTunes\\iTunes.exe"=
"c:\\Documents and Settings\\Dennis\\Local Settings\\Application Data\\Google\\Chrome\\Application\\chrome.exe"=
"c:\\Program Files\\McAfee\\VirusScan\\mcvsmap.exe"=
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"1700:TCP"= 1700:TCP:MioNet Remote Drive Access 0
"1701:TCP"= 1701:TCP:MioNet Remote Drive Access 1
"1702:TCP"= 1702:TCP:MioNet Remote Drive Access 2
"1703:TCP"= 1703:TCP:MioNet Remote Drive Access 3
"1704:TCP"= 1704:TCP:MioNet Remote Drive Access 4
"1705:TCP"= 1705:TCP:MioNet Remote Drive Access 5
"1706:TCP"= 1706:TCP:MioNet Remote Drive Access 6
"1707:TCP"= 1707:TCP:MioNet Remote Drive Access 7
"1708:TCP"= 1708:TCP:MioNet Remote Drive Access 8
"1709:TCP"= 1709:TCP:MioNet Remote Drive Access 9
"1641:TCP"= 1641:TCP:MioNet Remote Drive Verification
"1647:TCP"= 1647:TCP:MioNet Storage Device Configuration
"5432:UDP"= 5432:UDP:MioNet Storage Device Discovery
R0 si3112r;Silicon Image SiI 3112 SATARaid Controller;c:\windows\system32\drivers\SI3112r.sys [9/10/2006 11:05 AM 116264]
R0 SiWinAcc;SiWinAcc;c:\windows\system32\drivers\SiWinAcc.sys [9/10/2006 11:05 AM 19240]
R0 szkg5;szkg;c:\windows\system32\drivers\SZKG.sys [5/12/2009 2:13 PM 61328]
R3 LCcfltr;Logitech USB Filter Driver;c:\windows\system32\drivers\LCcfltr.sys [9/13/2006 11:36 PM 14095]
S2 MemeoBackgroundService;MemeoBackgroundService;c:\program files\WD\WD Anywhere Backup\MemeoBackgroundService.exe [4/17/2009 12:51 PM 25824]
S2 MioNet;MioNet;c:\program files\MioNet\MioNetManager.exe [1/14/2008 3:14 PM 139264]
S3 lgatbus;LG USB Composite Device driver (WDM);c:\windows\system32\drivers\lgatbus.sys [3/16/2009 6:10 PM 43024]
S3 lgatmdm;LG CDMA USB Modem Drivers;c:\windows\system32\drivers\lgatmdm.sys [3/16/2009 6:11 PM 77104]
S3 lgatserd;LG CDMA USB Modem Diagnostic Serial Port Drivers (WDM);c:\windows\system32\drivers\lgatserd.sys [3/16/2009 6:11 PM 60816]
S3 motccgp;Motorola USB Composite Device Driver;c:\windows\system32\drivers\motccgp.sys [3/18/2009 8:55 PM 18688]
S3 motccgpfl;MotCcgpFlService;c:\windows\system32\drivers\motccgpfl.sys [3/18/2009 8:55 PM 8320]
S3 MotDev;Motorola Inc. USB Device;c:\windows\system32\drivers\motodrv.sys [3/18/2009 8:55 PM 42112]
S3 Sus2pl;Susteen Universal Cable II;c:\windows\system32\drivers\sus2pl.sys [3/31/2004 3:33 PM 43392]
[HKEY_LOCAL_MACHINE\software\microsoft\active setup\installed components\>{60B49E34-C7CC-11D0-8953-00A0C90347FF}]
"c:\windows\system32\rundll32.exe" "c:\windows\system32\iedkcs32.dll",BrandIEActiveSetup SIGNUP
.
Contents of the 'Scheduled Tasks' folder
2009-09-24 c:\windows\Tasks\AppleSoftwareUpdate.job
- c:\program files\Apple Software Update\SoftwareUpdate.exe [2008-07-30 17:34]
2009-09-24 c:\windows\Tasks\GoogleUpdateTaskUserS-1-5-21-682003330-1563985344-839522115-1003Core.job
- c:\documents and settings\Dennis\Local Settings\Application Data\Google\Update\GoogleUpdate.exe [2009-03-15 17:14]
2009-09-24 c:\windows\Tasks\GoogleUpdateTaskUserS-1-5-21-682003330-1563985344-839522115-1003UA.job
- c:\documents and settings\Dennis\Local Settings\Application Data\Google\Update\GoogleUpdate.exe [2009-03-15 17:14]
2009-09-27 c:\windows\Tasks\McDefragTask.job
- c:\progra~1\mcafee\mqc\QcConsol.exe [2009-09-27 02:26]
2009-09-27 c:\windows\Tasks\McQcTask.job
- c:\progra~1\mcafee\mqc\QcConsol.exe [2009-09-27 02:26]
2009-09-24 c:\windows\Tasks\SDMsgUpdate (TE).job
- c:\progra~1\SMARTD~1\Messages\SDNotify.exe [2009-06-12 14:29]
.
.
------- Supplementary Scan -------
.
uStart Page = hxxp://www.google.com/ig
uInternet Settings,ProxyOverride = *.local
uSearchURL,(Default) = hxxp://www.google.com/keyword/%s
IE: E&xport to Microsoft Excel - c:\progra~1\MICROS~2\Office10\EXCEL.EXE/3000
.
**************************************************************************
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2009-09-27 15:36
Windows 5.1.2600 Service Pack 3 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
--------------------- DLLs Loaded Under Running Processes ---------------------
- - - - - - - > 'winlogon.exe'(1272)
c:\windows\system32\Ati2evxx.dll
.
Completion time: 2009-09-27 15:40
ComboFix-quarantined-files.txt 2009-09-27 20:39
ComboFix2.txt 2009-09-27 19:33
Pre-Run: 33,868,689,408 bytes free
Post-Run: 33,834,926,080 bytes free
Current=2 Default=2 Failed=1 LastKnownGood=4 Sets=1,2,3,4
289 --- E O F --- 2009-09-27 04:32
Upload was successful
Malwarebytes' Anti-Malware 1.41
Database version: 2866
Windows 5.1.2600 Service Pack 3
9/27/2009 3:55:46 PM
mbam-log-2009-09-27 (15-55-46).txt
Scan type: Quick Scan
Objects scanned: 107502
Time elapsed: 4 minute(s), 14 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 0
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
(No malicious items detected)
--------------------------------------------------------------------------------
KASPERSKY ONLINE SCANNER 7.0: scan report
Monday, September 28, 2009
Operating system: Microsoft Windows XP Professional Service Pack 3 (build 2600)
Kaspersky Online Scanner version: 7.0.26.13
Last database update: Monday, September 28, 2009 15:54:36
Records in database: 2930131
--------------------------------------------------------------------------------
Scan settings:
scan using the following database: extended
Scan archives: yes
Scan e-mail databases: yes
Scan area - My Computer:
C:\
D:\
E:\
F:\
G:\
Z:\
Scan statistics:
Objects scanned: 158345
Threats found: 8
Infected objects found: 15
Suspicious objects found: 0
Scan duration: 06:51:32
File name / Threat / Threats count
C:\Program Files\Dvd-cloner\Dvd-cloner4.exe Infected: Trojan-Dropper.Win32.Delf.dxg 1
D:\AADownloads\DVD Burning\dcloner.exe Infected: Trojan-Dropper.Win32.Delf.dxg 1
D:\AADownloads\RingTones\Download_cwrtinst.exe Infected: not-a-virus:Downloader.Win32.SpyNoMore.a 1
D:\Mail\Mail\mail.alltel-1.net\Inbox Infected: Trojan-Dropper.VBS.Zerolin 1
D:\Mail\Mail\mail.alltel-1.net\Trash Infected: Trojan-Dropper.VBS.Zerolin 1
D:\Mail\Mail\mail.comcast-1.net\Inbox Infected: Exploit.HTML.CodeBaseExec 1
D:\Mail\Mail\mail.comcast-1.net\Inbox Infected: Email-Worm.Win32.Bagle.al 1
D:\Mail\Mail\mail.comcast-1.net\Inbox Infected: Trojan-Spy.HTML.Bankfraud.fl 1
D:\Mail\Mail\mail.comcast.net\Inbox Infected: Exploit.HTML.CodeBaseExec 1
D:\Mail\Mail\mail.comcast.net\Inbox Infected: Email-Worm.Win32.Bagle.al 1
D:\Mail\Mail\mail.comcast.net\Inbox Infected: Trojan-Spy.HTML.Bankfraud.fl 1
D:\Mail\Mail\mail.comcast.net\Sent Infected: Trojan-Spy.HTML.Bankfraud.fl 1
D:\Mail\Mail\mail.comcast.net\Trash Infected: Trojan-Spy.HTML.Bankfraud.fl 1
D:\Work (Honeywell)\My_Data\Outlook PST Files\Personal Files (PST)\DSTONE1.PST Infected: Email-Worm.VBS.Homepage 1
D:\Work (Honeywell)\My_Data\Outlook PST Files\Personal Files (PST)\DSTONE1.PST Infected: Email-Worm.VBS.Scrapworm 1
Selected area has been scanned.
Register to Remove
#11
![[Resolved] Computer Hijacked: post #11](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 28 September 2009 - 06:44 PM
Please do the following:
- Go to Start->Run and type in notepad and hit OK.
- Then copy and paste the content of the following codebox into Notepad:
@echo off if exist "%temp%\log.txt" del "%temp%\log.txt" for %%g in ( "C:\Program Files\Dvd-cloner\Dvd-cloner4.exe" "D:\AADownloads\DVD Burning\dcloner.exe" "D:\AADownloads\RingTones\Download_cwrtinst.exe" ) do ( del /a/f/q %%g if exist %%g echo.%%g >>"%temp%\log.txt" )>nul 2>&1 if exist "%temp%\log.txt" (start notepad "%temp%\log.txt" ) else echo.Deleted Successfully! echo. pause del %0
- Save the file to your DESKTOP as "find.bat". Make sure to save it with the quotes.
- Once saved, the icon to click should look like this on your desktop:
- Double click find.bat. to run it. A small black box should open and close - this is normal.
- A notepad file will open, please copy/paste the content in your next reply.
The other items found by Kaspersky are in your email, you need to look through them and delete anything from anyone you don't know or any with attachment, as Kaspersky is unable to determine which particular emails are infected.
NEXT
Please post a fresh DDS Log and attach.txt and advise how your computer is running now and if there are any outstanding issues.
Microsoft MVP 2010, 2011, 2012, 2013, 2014, 2015
#12
![[Resolved] Computer Hijacked: post #12](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 28 September 2009 - 07:19 PM
#13
![[Resolved] Computer Hijacked: post #13](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 28 September 2009 - 08:20 PM
Attached Files
#14
![[Resolved] Computer Hijacked: post #14](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 28 September 2009 - 08:39 PM
There are a couple more files to delete, then we can do our final cleanup.
Please do the following:
- Go to Start->Run and type in notepad and hit OK.
- Then copy and paste the content of the following codebox into Notepad:
@echo off if exist "%temp%\log.txt" del "%temp%\log.txt" for %%g in ( "c:\windows\kuxeg.db" "c:\windows\system32\ozuqy.lib" "c:\windows\system32\lidene.lib" "c:\windows\system32\fibogenuju.lib" "c:\windows\system32\3a54A.tmp" "c:\windows\system32\c9e48.mht" "c:\windows\system32\ijomytydi.db" "c:\windows\hyxyni.db" ) do ( del /a/f/q %%g if exist %%g echo.%%g >>"%temp%\log.txt" )>nul 2>&1 if exist "%temp%\log.txt" (start notepad "%temp%\log.txt" ) else echo.Deleted Successfully! echo. pause del %0
- Save the file to your DESKTOP as "find.bat". Make sure to save it with the quotes.
- Once saved, the icon to click should look like this on your desktop:
- Double click find.bat. to run it. A small black box should open and close - this is normal.
- Let me know if it deletes successfully.
NEXT:
Visit ADOBEand download the latest version of Acrobat Reader (version 9.1)
Having the latest updates ensures there are no security vulnerabilities in your system.
NEXT:
Please download JavaRa to your desktop and unzip it to its own folder.
- Run JavaRa.exe, pick the language of your choice and click Select. Then click Remove Older Versions
- Accept any prompts.
- Open JavaRa.exe again and select Search For Updates.
- Select Update Using Sun Java's Website then click Search and click on the Open Webpage button.
- Scroll down to the Java SE Runtime Environment (JRE) option.
- Download and install the latest Java Runtime Environment (JRE) version for your computer.(version 6, update 16)
NEXT
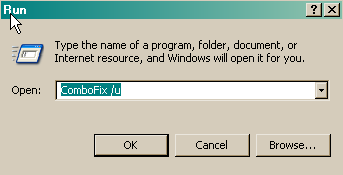
Follow these steps to uninstall Combofix
- Click START then RUN
- Now type Combofix /u in the runbox and click OK. Note the space between the ..X and the /U, it needs to be there.
NEXT
Now to remove the rest of the tools that we have used in fixing your machine:
- Make sure you have an Internet Connection.
- Download OTC to your desktop and run it
- A list of tool components used in the Cleanup of malware will be downloaded.
- If your Firewall or Real Time protection attempts to block OTC to reach the Internet, please allow the application to do so.
- Click Yes to begin the Cleanup process and remove these components, including this application.
- You will be asked to reboot the machine to finish the Cleanup process. If you are asked to reboot the machine choose Yes.
If there are any other logs/tools remaining, just right click and delete them.
NEXT
Below I have included a number of recommendations for how to protect your computer against malware infections.
- It is good security practice to change your passwords to all your online accounts on a fairly regular basis, this is especially true after an infection. Refer to this Microsoft article
Strong passwords: How to create and use them
Then consider a password keeper, to keep all your passwords safe.
- Keep Windows updated by regularly checking their website at :
http://windowsupdate.microsoft.com/
This will ensure your computer has always the latest security updates available installed on your computer.
- SpywareBlaster protects against bad ActiveX, it immunizes your PC against them.
- SpywareGuard offers realtime protection from spyware installation attempts. Make sure you are only running one real-time anti-spyware protection program ( eg : TeaTimer, Windows Defender ) or there will be a conflict.
- Make Internet Explorer more secure
- Click Start > Run
- Type Inetcpl.cpl & click OK
- Click on the Security tab
- Click Reset all zones to default level
- Make sure the Internet Zone is selected & Click Custom level
- In the ActiveX section, set the first two options ("Download signed and unsigned ActiveX controls) to "Prompt", and ("Initialize and Script ActiveX controls not marked as safe") to "Disable".
- Next Click OK, then Apply button and then OK to exit the Internet Properties page.
- ATF Cleaner - Cleans temporary files from IE and Windows, empties the recycle bin and more. Great tool to help speed up your computer and knock out those nasties that like to reside in the temp folders.
- MVPS Hosts file replaces your current HOSTS file with one containing well known ad sites and other bad sites. Basically, this prevents your computer from connecting to those sites by redirecting them to 127.0.0.1 which is your local computer, meaning it will be difficult to infect yourself in the future.
WOT, Web of Trust, warns you about risky websites that try to scam visitors, deliver malware or send spam. Protect your computer against online threats by using WOT as your front-line layer of protection when browsing or searching in unfamiliar territory. WOT's color-coded icons show you ratings for 21 million websites, helping you avoid the dangerous sites:- Green to go
- Yellow for caution
- Red to stop
- For Firefox, I highly recommend this add-on to keep your PC even more secure.
- NoScript - for blocking ads and other potential website attacks
- Keep a backup of your important files - Now, more than ever, it's especially important to protect your digital files and memories. This article is full of good information on alternatives for home backup solutions.
- ERUNT (Emergency Recovery Utility NT) allows you to keep a complete backup of your registry and restore it when needed. The standard registry backup options that come with Windows back up most of the registry but not all of it. ERUNT however creates a complete backup set, including the Security hive and user related sections. ERUNT is easy to use and since it creates a full backup, there are no options or choices other than to select the location of the backup files. The backup set includes a small executable that will launch the registry restore if needed.
- In light of your recent issue, I'm sure you'd like to avoid any future infections. Please take a look at these well written articles:
Think Prevention.
PC Safety and Security--What Do I Need?.
**Be very wary with any security software that is advertised in popups or in other ways. They are not only usually of no use, but often have malware in them.
Thank you for your patience, and performing all of the procedures requested.
Please respond one last time so we can consider the thread resolved and close it, thank-you.
Microsoft MVP 2010, 2011, 2012, 2013, 2014, 2015
#15
![[Resolved] Computer Hijacked: post #15](https://forums.whatthetech.com/public/style_images/smart34xbuild2/icon_share.png)
Posted 28 September 2009 - 10:22 PM
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users



 This topic is locked
This topic is locked




